3.1 Control Plane vs Agent Execution Plane
3.2 Project Scope Model
3.3 Data Flow: Source -> Release -> Pipeline -> Logs/Artifacts
3.4 Runtime Configuration Layers (global / project / environment)
3.5 Pipeline Execution Semantics
3.6 Release Governance Path
3.7 Rollback Architecture (Policy-driven)
3.8 Security and Trust Boundaries
3.9 State and Persistence Model
3.10 Scalability Model
3.11 Failure Modes and Recovery Patterns
3.12 Why This Architecture Works in Practice
16.4 API Keys
Orbnetes deployment and release orchestration documentation for operators and platform teams.
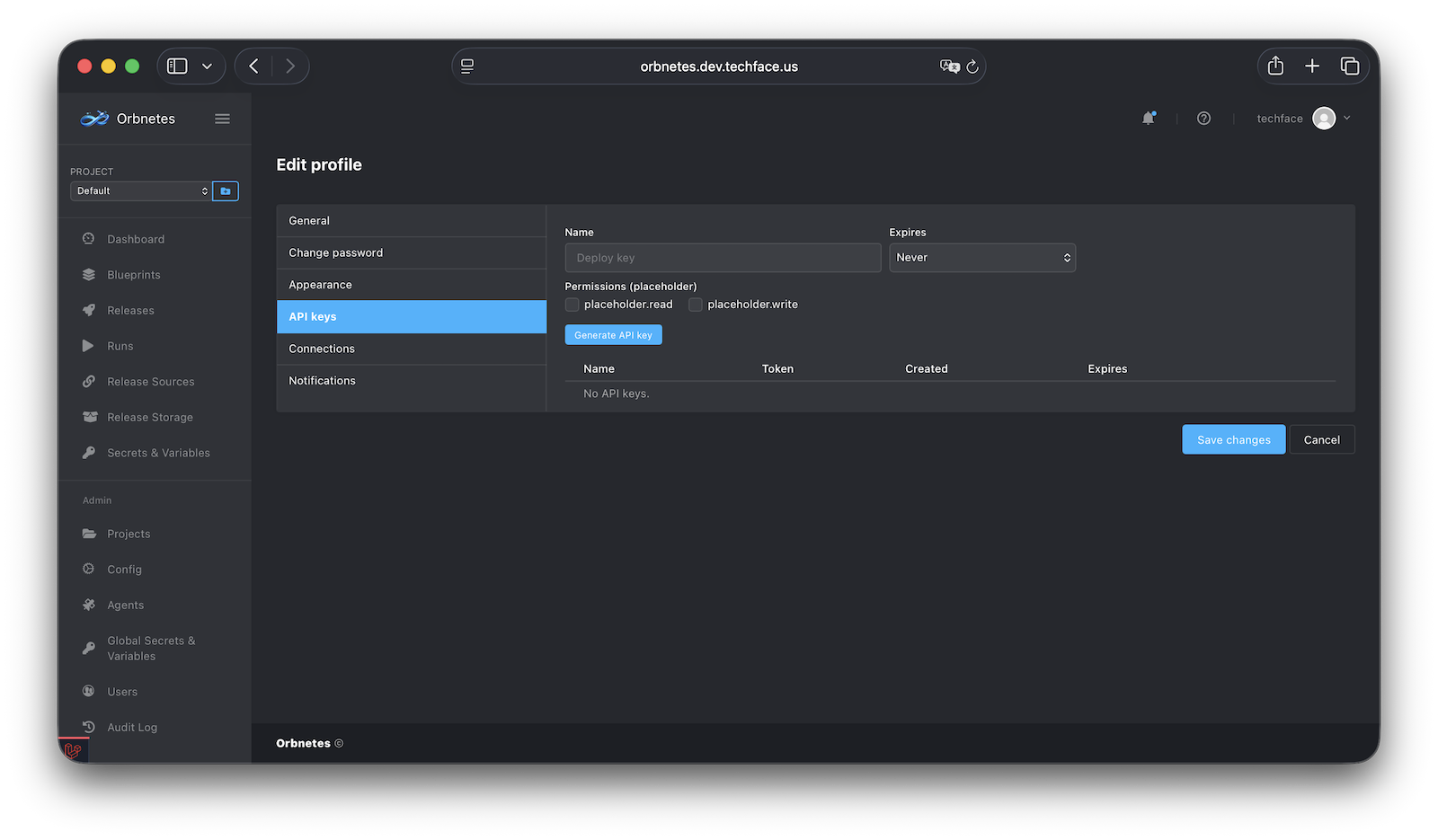
API keys allow non-browser automation to act on behalf of a user (subject to key/user permissions).
Typical model:
- user generates key in profile,
- key is shown once at creation,
- key can have expiration (
neveror specific date/time), - key can be revoked/deleted.
Security principles:
- treat API key like secret credential,
- store only in secure secret managers,
- do not paste into logs, tickets, or YAML files,
- rotate regularly and revoke on suspicion.
Operational recommendations:
- use separate keys per integration/service,
- prefer short-lived keys where practical,
- tag/document key ownership and purpose internally.