3.1 Control Plane vs Agent Execution Plane
3.2 Project Scope Model
3.3 Data Flow: Source -> Release -> Pipeline -> Logs/Artifacts
3.4 Runtime Configuration Layers (global / project / environment)
3.5 Pipeline Execution Semantics
3.6 Release Governance Path
3.7 Rollback Architecture (Policy-driven)
3.8 Security and Trust Boundaries
3.9 State and Persistence Model
3.10 Scalability Model
3.11 Failure Modes and Recovery Patterns
3.12 Why This Architecture Works in Practice
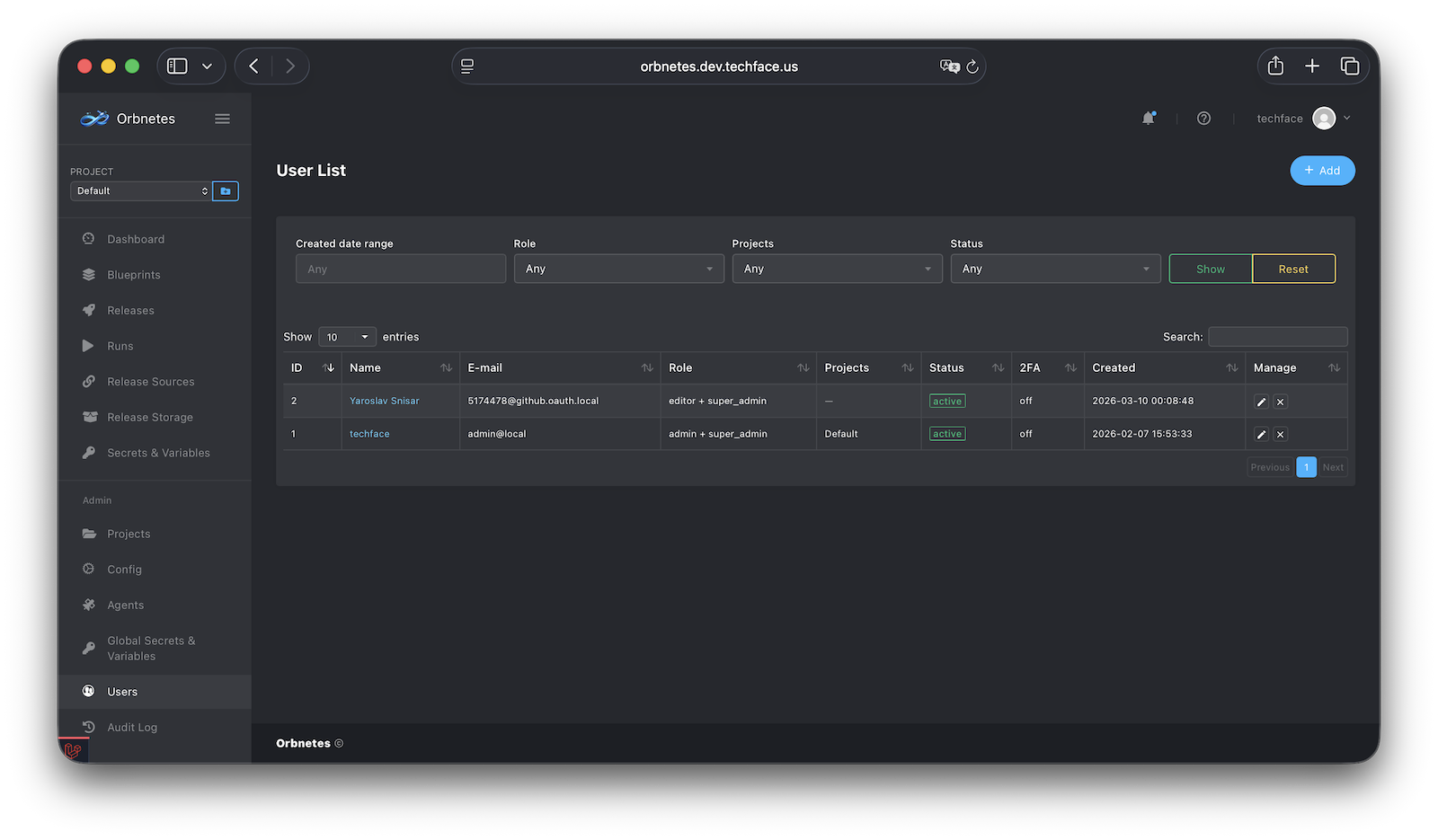
16.1 User Model and Profile
Orbnetes deployment and release orchestration documentation for operators and platform teams.
This section defines how identity and authorization work in Orbnetes. The security model combines:
- user identity (local and OAuth),
- project-scoped permissions,
- global permissions for platform-level operations,
- optional API keys,
- optional 2FA requirements.
Design objective:
- least privilege by default,
- clear separation between project operations and platform administration,
- auditable actor identity for sensitive actions.
Each user account represents an operational actor in the platform.
Typical user attributes:
- name and username,
- login identity (email/local and/or OAuth connections),
- profile metadata (company/org, contact fields, preferences),
- auth status (active/pending/blocked depending on policy),
- avatar and appearance preferences.
Profile capabilities usually include:
- self-editable profile data,
- password change (for local auth),
- 2FA setup/reconfigure,
- API key management,
- connected OAuth providers.
Operational significance:
- actor identity is used in release/run/audit attribution,
- profile-level notification settings define personal delivery preferences,
- user status affects access to all operational surfaces.